Hi and welcome back!
Today we will talk about Privileged Identity Management (PIM) and I will show you the idea of how you can enable this for your admin users in your tenant.
First – what is a Microsoft Entra role and why can’t all your admins just be Global Admins 24/7?!?
Microsoft states; “In Microsoft Entra ID, if another administrator or non-administrator needs to manage Microsoft Entra resources, you assign them a Microsoft Entra role that provides the permissions they need. For example, you can assign roles to allow adding or changing users, resetting user passwords, managing user licenses, or managing domain names.” (Microsoft Entra built-in roles – Microsoft Entra ID | Microsoft Learn)
Thinking Least Privilege, you don’t really need admin roles 24/7, do you? You would want your admins to just have the permission they need to do the task they need to perform at exactly the moment they are going to execute it, right? That’s PIM in a nutshell. The improvement actions for Defender For Identity also includes a task called “Use least privileged administrative roles” – so we will increase our secure score with this one as well – yay!
So how many roles do we have? A lot! And the link above lists them all, explain what they can do and highlights the ones considered a “Privileged Role”. Microsoft states that a “Privileged Role” is “roles and permissions can be used to delegate management of directory resources to other users, modify credentials, authentication or authorization policies, or access restricted data. Privileged role assignments can lead to elevation of privilege if not used in a secure and intended manner.”
In other words, they should be handled and delegated with great care. For more detailed permissions on those, have a looksie here; Privileged roles and permissions in Microsoft Entra ID (preview) – Microsoft Entra ID | Microsoft Learn
But let’s get back to PIM and what this is all about. In this scenario we want to do the following.
- Define the Role settings on one of the roles so it will give you an idea on how to do that on all the roles
- Add one role-assignment to give you an idea on how to setup the different assignments for the roles you want to make available for your admins.
- Make an “Access Review” for a role to give you the idea on how and why you should actively review these assignments.
Locate PIM in the portal.
Locate “Microsoft Entra roles”.
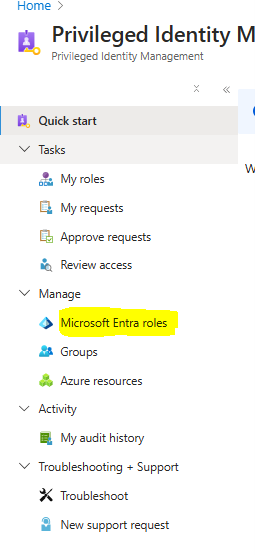
Under “Manage”, locate “Roles”.

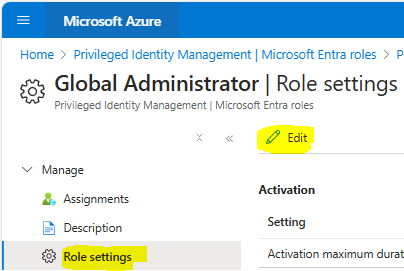
Click on the role you want to review – in this scenario we will check the Global Administrator role. Go to “Role Settings” and press “Edit”.
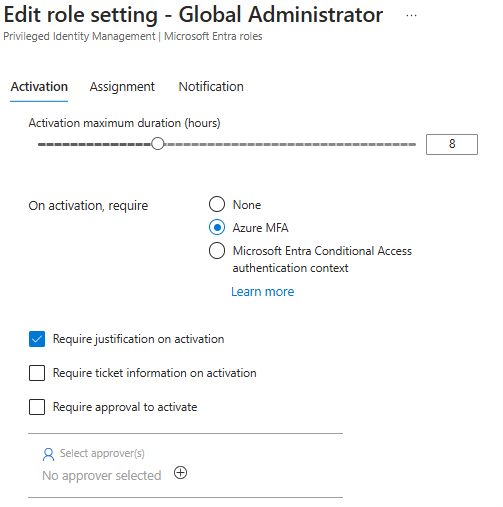
So, what settings can we perform on page 1? You can choose for how long the activation can last before the user needs to perform the activation again, you can set a requirement for MFA on activation, if the user needs to add a justification, ticket information or an approval to activate. In this scenario, we will go for the proposed 8 hours, we will choose Azure MFA (since we haven’t setup or covered CA-authentication context yet), and we want the user to add a justification when activating. Note to self; inform your admin users to actually writhe the tasks going to be performed in the justification as this is getting logged and could be useful in an audit.
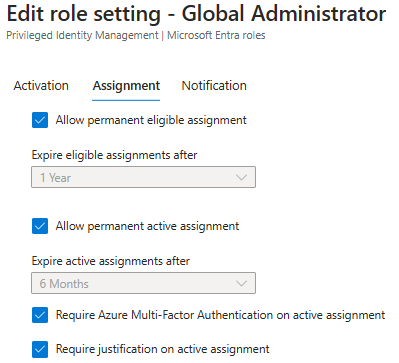
On the next page, you can choose if this assignment should be available as a permanent active, an eligible, a permanent eligible assignment, if they should ever expire automatically and if you want to require MFA and justification on active assignments as well. In this scenario we want this to be both available as a permanent active assignment for our BreakGlass accounts and as a permanent eligible assignment for our admin user. (What is a BreakGlass account and how to set it up; …blogpost in the making…)
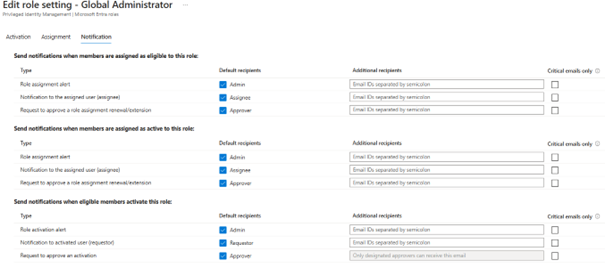
Before we update the role-settings, we can choose to send notifications when members are assigned as eligible, when members are assigned as active and when eligible members activate this role. This could be a good way to get notified – but I should warn you that this will generate a lot of mails on a day-to-day basis if you are quit a few admins. I do not have the correct answer for you here, but you should absolutely have the discussion on this. Who should be informed and why on activation?
In this scenario, I will leave it at default.
When the settings is where you want them to be, you can go back and assign them.
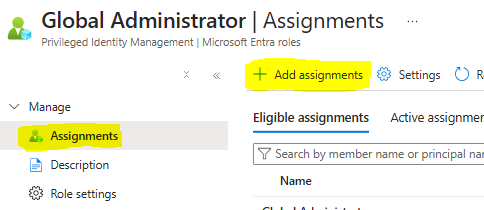
Press “+ Add assignments” and choose the user you want to add the assignment to.
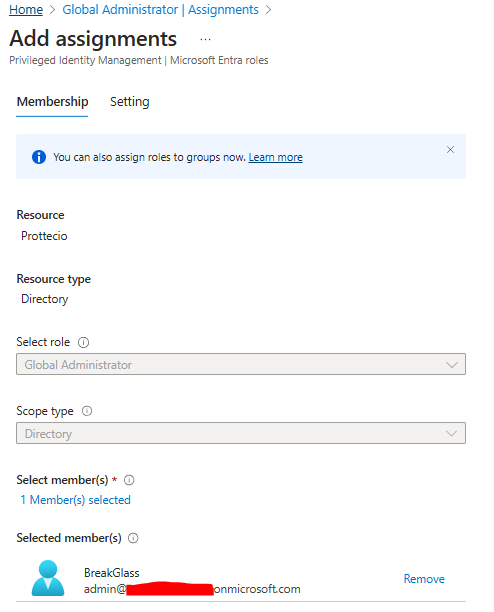
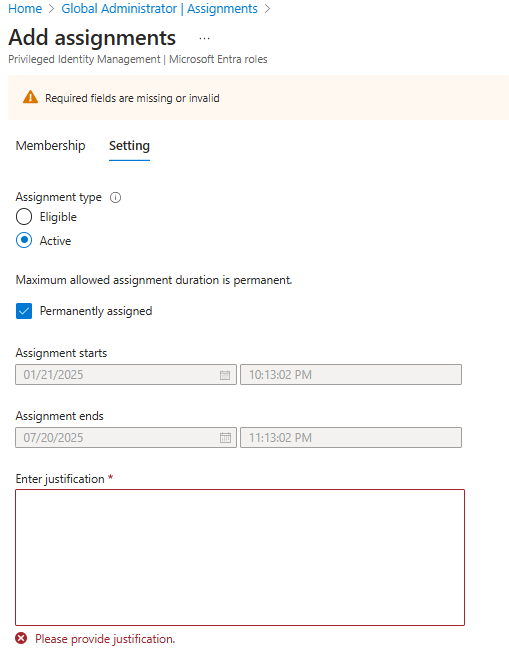
On the next page you have to choose if this is an eligible or active assignment and if it’s going to be permanent or have a start/stop time. In this scenario, we want to assign the Global Admin role as a permanent active role to the BreakGlass-account.
When it’s done, you can check that it’s active here.
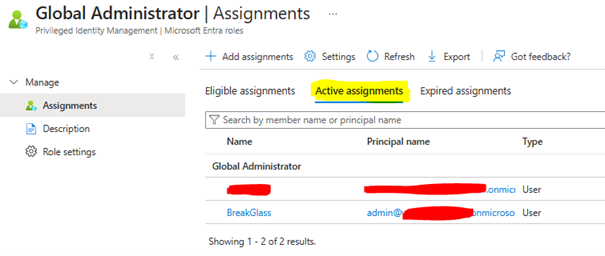
As you can see there is two users there. I’ve also added a second assignment which is permanently eligible for my day-to-day admin user. So, when that user logs in to the portal.azure.com and locates PIM, he is faced with this.
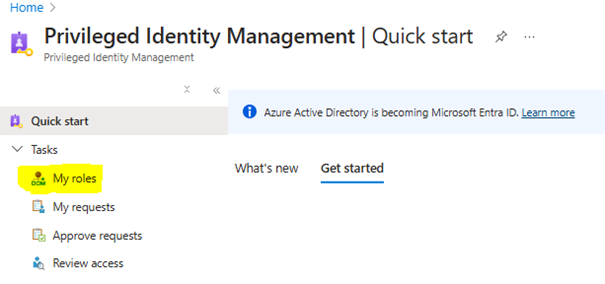
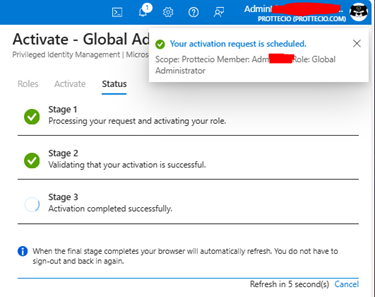
I will go to “My roles”, press “Activate” on the role I want to activate, and I will have to set the duration and write a short justification.
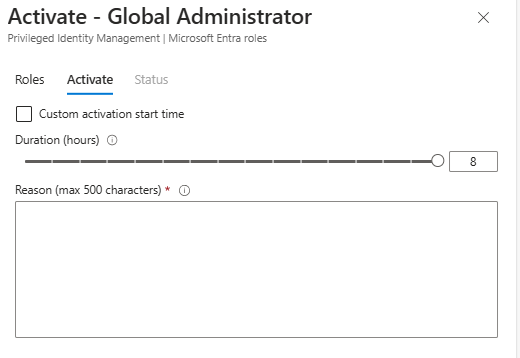
After hitting “Activate” it will perform a check if I’m eligible for the role and activate it.
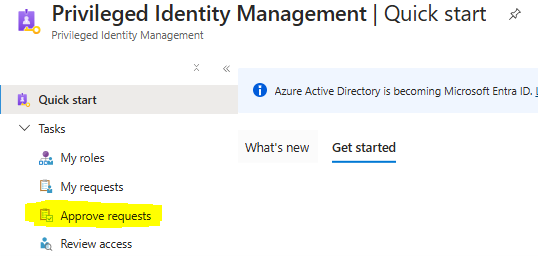
If we were to choose that it needed approval in the settings, the approver will find the waiting request here.
That’s it! Really easy to be honest – but it gives you better control over your admin roles and who can elevate in my opinion. A must-do to get rid of 24/7 privileged permissions on your admin users.
But let’s not forget to add an “Access Review”.
Because suddenly another admin user needs a new role for a specific task, and you forget to put an end date on the assignment. The access review comes to your aid!
In the main menu for PIM, locate “Microsoft Entra roles” under “Manage” and from there locate “Access reviews” under “Manage”
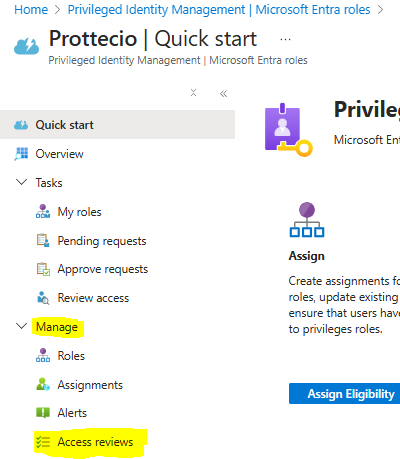
In this scenario, we want to make an Access Review for the Global Admin role. I would advise to make these for all roles that you’ve made assignments for. I think the best-practice advice would be to perform this every 90-days – but I would say at least once a month, especially for privileged roles.
Give it a name, a description, set the start day, set the frequency and duration (in days) and if you want it to have an end date. Select the user scope, what role(s) you want to review, the assignment types and who should be the reviewers.
Upon completion settings you can choose to auto-apply the results, what to happen if the reviewers don’t respond, whom to send notifications to after the review – and in the advanced settings you can choose to get recommendations, require reason on approval, mail notifications, reminders and additional content for the reviewer email. Pretty straight forward in other words.
This link explain these settings in detail, so I won’t; Create an access review of Azure resource and Microsoft Entra roles in PIM – Microsoft Entra ID Governance | Microsoft Learn
There you go – we’ve made another security improvement to our tenant and something you can and should perform now if you haven’t.
Good luck and hope to see you next time!

