It’s been too long since my last post. Life caught up to me, so did work. It’s been a long 1,5 years, to cut it short I acted as IT-leader in Voss herad (a municipality in Norway) from June 2023 to June 2024 before I then got the job and title permanently. A big task, a big responsibility and a big opportunity – right now I wouldn’t be any other place then working with my talented IT-crew here – we have done a lot of good work the last couple of years and we have a lot of cool stuff on the threshold for 2025!
The blog has been lurking in the back of my head but I just couldn’t find enough time to do it right, so I didn’t. The way I started out I wanted to do a scenario from A-Z with all details covered. A way bigger project than I first thought it to be.
But a couple of weeks ago, after posting a bit on LinkedIn about FIDO and phishing-resistant authentication, I stated something along the line; “don’t wait to implement something security related just because you can’t do it 100% the first time – it’s better to do something than nothing at all. 10% is better than 0%”

That got me thinking on an issue I don’t think I’m alone with. Overthinking and postponing important security implementations just because you want it to be 100% instead of actually improve it by 10%. So why don’t switch the focus on this blog to help others go from “zero-to-hero” in their security posture? Start with a fresh test-tenant and just see how fast and “easy” you can go from 0% to 100% on the Secure Score?
Let’s be honest – we probably won’t see the 100 mark – but let’s aim for at least 90%!
So how shall we do it?
I have a fresh new test-tenant, Microsoft Entra ID P2 licensed. What I have done already is to set up CA’s (conditional access policies) requiring MFA on admin accounts, I activated PIM on the admin-accounts, and I created a Break glass (BG) account to not lock myself out. Other than that, it’s pretty empty.
From here we will go through some quick and cool stuff to improve general security. We will cover CA’s, MFA and phishing-resistant authentication, PIM, BG-accounts and more! Most importantly, we will dig into Microsoft Secure Score. Depending on your licensing and your environment, that will really help reducing your attack surface, removing vulnerabilities and improve your company’s security posture! For more information, check the documentation here; https://learn.microsoft.com/en-us/defender-xdr/microsoft-secure-score
And that is what security is all about in my opinion. Layers upon layers upon layers. Not one big setting, but several to make the attacker give up, and you a chance to discover and handle the attack. The sooner you realize that your job is not to reach a 100% security posture and stop every attack coming, the more fun it will be. Your job is (amongst others) to implement a security posture good enough to slow down the attacker and discover it soon enough to minimize the damage and outage, be able to isolate it and maintain up-time.

The environment
Since my test-tenant is so new and small and don’t have the licensing, onboarded devices or created a lot of users yet, I will export the different security recommendations from a larger production environment. Just to compare, my test-tenant has 16 recommendations from the start, whilst one of the production tenant I help administrate had 258 recommendations…
If your Secure Score does not show all 4 categories (Identity, Data, Device and Apps) – you may not have the correct licensing or you have some lacking configuration. You may also have to visit the Purview-portal, enroll a device into Intune and Defender – and it may also take some time before all the controls are coming to your overview. I left it for a couple of days and now my recommended actions shows 74 items – yay!
IMPORTANT NOTICE – I will try to explain what impact the settings will have in a big environment – but you should always test these settings in a test-environment or on a small group of users/devices before going big-scale.
So how does the recommendations look?
If you use the defender portal and click on the recommendation, you will get a good description on what it is and what it will do, what the user impact is, prerequisites, step-by-step guides and reference to the documentation.
In my test-tenant it now looks like this;
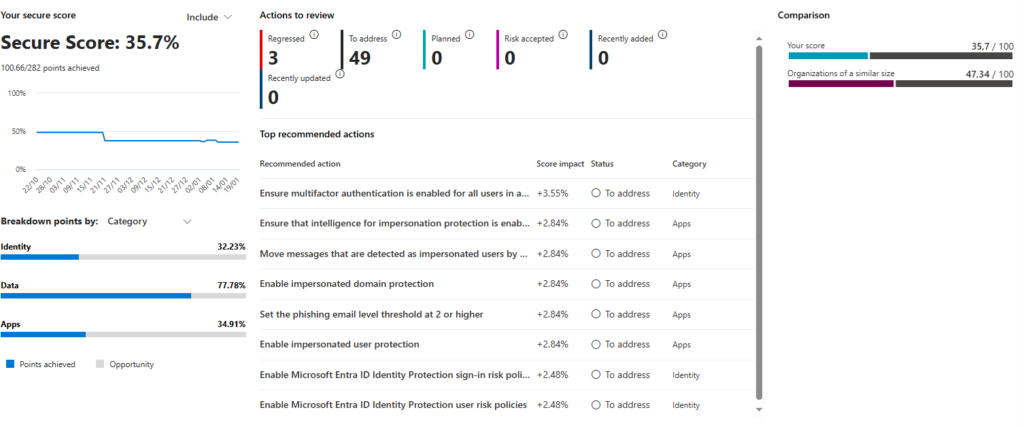
Pretty overwhelming, right? But don’t worry, we will break it down and make it manageable so we can start our journey from hero to zero!
Some of them will be solve together as well as they are in the same policy setting.
So hope to see you next time on the next blog post; “2025 – Enable Phishing-resistant MFA in your tenant”


